Leveraging National Cybersecurity Awareness Month for Continuous Employee Training
Each October, National Cybersecurity Awareness Month (NCSAM) reminds us just how important IT security is both at work and at home.
It’s also a great catalyst for planning your ongoing cybersecurity training throughout the year for employees, because cyberattacks happen year-round. Security awareness training is not a “one-month” thing, but rather an “all-year-round” activity.
Here are a few statistics that Massachusetts businesses need to be aware of:
- There’s been a seven-fold increase this year in the number of ransomware attacks, compared to 2019.
- IoT threats rose by 35% in the first half of 2020 compared to the last half of 2019.
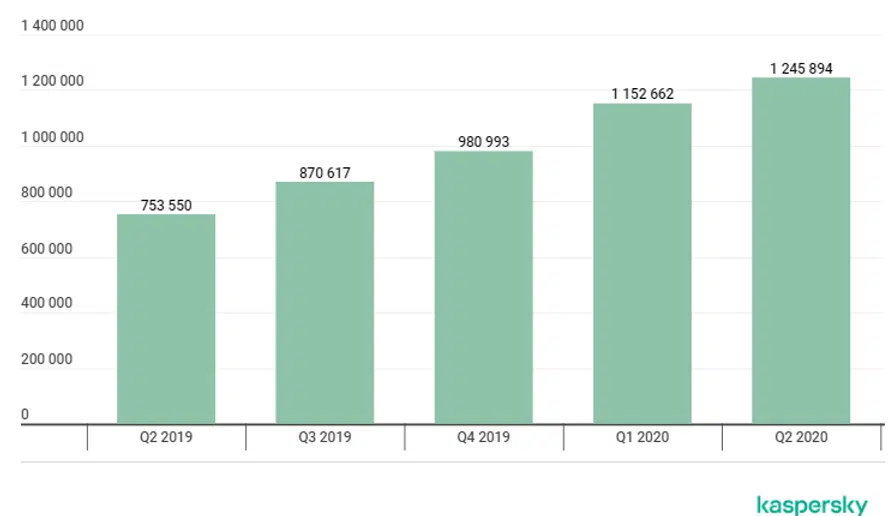
- Mobile security attacks have continued to rise each quarter between Q2 2019 and Q2 2020.
Why Ongoing Employee Cybersecurity Awareness Training is Important
If you’re only mentioning cybersecurity to your employees once in a while, then you’re leaving your business at risk of phishing attacks, data security incidents, and other potential problems.
When employees are trained consistently on cybersecurity awareness, the chance of successful attack is significantly reduced. Ongoing employee training should include a mixture of training in different areas, regular reminders about cybersecurity best practices, and the use of a variety of training tools (videos, tip sheets, webinars, etc.).
By leveraging the theme and resources of National Cybersecurity Awareness Month, you can keep your training fresh and timely all year-round.
Resources to Promote Cybersecurity
You’ll find a wide range of tip sheets and other resources to leverage at the NSCAM website. Here are tips on how to use these in your employee awareness training.
1. Promote Responsibility with the Message: “If You Connect It, Protect It.”
The primary message of this year’s NCSAM relates to the fact that everyone shares responsibility for cybersecurity within an organization.
Use the “If You Connect It, Protect It” theme throughout the year to remind employees of things they can do to protect the devices they’re using and take personal responsibility for staying safe.
This can include things like:
- Being on the lookout for phishing when using email
- Using screen locks with passcodes on devices
- Keeping device OS, software, and apps updated
2. Review Device Security at Work
Use the NCSAM Cybersecurity at Work tip sheet to promote best practices for keeping company data, networks, and devices safe.
Hackers are relying on human error to gain access to sensitive data and accounts, which is why phishing has been the number one cause of malware infections and data breaches for years.
Promote tips like:
- Treating all company information as sensitive
- Using strong passwords
- Using multi-factor authentication (MFA) on all logins
- Remaining vigilant (all it takes is one wrong click to cause a data breach)
3. Promote Home Security for Remote Workers
77% of companies plan to keep some employees working from home 3+ days per week after the pandemic. This makes security for remote workers a high priority and something you should infuse into your employee cybersecurity training plan.
You can use this NCSAM tip sheet on Protecting Your Digital Home to offer guidance to your team about how to work safely from home.
It includes tips such as:
- Securing home Wi-Fi
- Being careful which mobile apps are downloaded
- Using MFA on device logins
- Being careful what information is shared over social media
4. Include Training on IoT Security
Internet of Things (IoT) devices are multiplying rapidly. Many homes and businesses now have several wireless devices that are attached to the network.
IoT devices include things like IP security cameras, routers, wireless printers, and more. The data transmitted and received by IoT gadgets is usually unencrypted, making them one of your riskiest endpoints.
You can promote smart gadget security by sharing the NCSAM Internet of Things tip sheet, along with best practices, such as:
- Immediately changing the username and password during set up of devices
- Keeping firmware updated regularly
- Creating a “guest” network and putting all IoT devices on that, separate from other devices (computers, servers, etc.)
- Using a device name that does not include model, brand, or location
Reduce Your Risk of a Major Cybersecurity Incident
Cleartech Group can assess your company’s current IT security strategy and let you know where any vulnerabilities exist. We’ll help you stay safe and avoid costly attacks.
Contact us today to discuss our cybersecurity options! Call us to chat at 978-466-1938 or reach out online.